What steps are you taking to keep your office premise secure? How are you ensuring that the visitors to your office complex get authorized access?
You may think your office is secure just having a receptionist/security guard enter the visitor details in a physical log book.
But such measures are inadequate to keep your workplace safe. You have to put something in place that can prevent unauthorized entries and register every visitor in a much more professional and smarter way.
As per a report, 19.4% firms all over the world have to face losses for cases of vandalism and theft.
Besides, your office security is not just threatened by theft- there have been many cases where suspects have tailgated or piggybacked an authorized person to illegally gain entry into restricted areas.
A survey by Boon EDAM security solutions found that 71% respondents believe there could be a medium to a significant security breach at their office due to tailgating.
An electronic visitor management system can be a great solution to boost your office security. Let’s find out some of the ways a visitor management system or VMS solution enables office admins and security teams to create a safer office premise without bordering genuine visitors with the hassle of filling in entries manually.
VMS is the Smarter Way to Boost Office Security
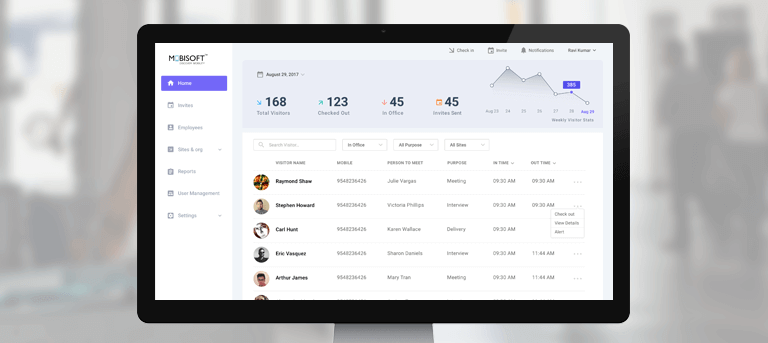
VMS is a software solution which replaces the old and ineffective paper-based visitor logbooks with slick iPad/tablet interfaces. You can collect required details from a visitor in a seamless manner, notify hosts, issue badges, ask for digital signatures, maintain a comprehensive database, automate workflows and a lot more to derive security benefits and greater efficiency.
Below are few ways in which a lobby/reception management system can enhance your organization’s security.
- Digital Visitor Logs

Digital visitor logs are effective on so many levels compared to paper-based visitor log books that you won’t be able to imagine. The handwriting can be illegible or difficult to read defeating the whole purpose of keeping a log. Collecting ID proofs can be a pain.
With digital visitor logs, you can scan information directly from ID proofs like driver’s license and have it entered automatically into a database through the VMS.
There is minimal chance of someone entering false information and you are guaranteed much higher accuracy. Along with accurate information, this stage also verifies the identity of your visitor automatically based on the ID proof.
The digital log book is able to store important details like check-in and checkout times. You can see who is in your building in real-time and even access the information later on to fetch reports.
The data can also be combined with analytics to derive patterns or insights on your visitor movement. All the data is stored in the VMS and you can search, retrieve and sort visitor data electronically at any time using an admin dashboard.
There is no need to turn through numerous pages and scan each entry manually!
- Visitor Badges

Your visitors must be issued badges/passes with critical information about them. It helps in identification and lets you know who is meant to be where.
Traditionally enterprises issue visitor passes but they are far from being effective in preventing security breaches. That’s where a VMS with connected visitor badge printing systems can help you out.
You can set up a VMS with a camera and printer and program it to print professional visitor badges.
The visitor badge can also be made to include vital information like the purpose of visit, time of entry, name of person intended to be visited and more.
You can even include your company logo for branding purpose and easier identification. Make your visitors carry this badge and educate your employees to alert the security team if anyone is seen without one.
- Digital Signature Capture

A visitor management system can be used to capture signatures digitally from visitors. You can place an iPad at the entry or reception on which anyone visiting your office needs to sign digitally as part of the check-in process.
The digital signature is stored in the system and can be used to verify future entries by the same person on repeat visits.
You can also print the signature on badges and use it for other references if you want. For example, the saved signature can be automatically used in other signing processes after verifying the identity of the person. You can automate any legal document signing process and NDAs by integrating them with your VMS.
- Private Visitor Records

In this age of internet and digital data, privacy has become one of the major concerns. All of us would want that our online information remains private and not inaccessible by unauthorized parties.
When we are so much concerned about our own privacy, why would you neglect that of your visitors?
In paper logbooks, anyone can see the list of previous visitors while writing down their own details. All the information is open and readable which leaves a big question on your visitor security and privacy.
The information can also be used for malicious activities and you don’t want that to happen!
In case of VMS data, information can only be accessed by people with prior permission or login credentials, which makes it more secure. Paper logs would be lying on tables and anyone could take a glance while passing by.
- Host Notifications

Do you like to wait sitting in the lobby when you are visiting someone?
Of course not! Yet you may have to wait because the person you want to meet is not aware that you are already there.
The benefits of a good visitor management system can help you tackle such a situation effectively.
You can program the VMS to automate message forwarding to alert the host employee as soon as the intended visitor signs in. In case of unavailability, the system automatically sends a message and alerts other available employees.
It presents a professional attitude and leaves a good impression on your clients or contractors.
- ITAR Compliance

VMS is also needed in enterprises for compliance and meeting regulatory policies. For example, some companies dealing in defense sector have to be compliant with International Traffic in Arms Regulations (ITAR).
There are many requirements to meet ITAR compliance, but we are only going to focus on the visitor management part. If your company falls under ITAR then you have to take care of the following
– Maintain a record of each and everyone who enters your premise.
– Have a documented visitor management process in place.
– Verify the citizenship of every visitor to confirm if they are residents of USA.
The above tasks call for a comprehensive visitor management system which can only be met with a digital solution. VMS with its visitor database stores all information about your visitors along with date and time stamps.
The whole process of visitor management is conducted by the VMS which meets the requirement of a documented process. You can also verify the identity easily in a hassle free way by scanning an ID proof automatically using a camera with your visitor management app.
You need a reliable VMS to meet ITAR compliance or face legal issues and compliance lapses.
- Efficient Evacuation During Emergencies

A VMS enables you to handle an emergency situation with more confidence as you have the power of real-time data. When a crisis arises, you can instantly view all the current visitors present in the building right at that given moment.
You can also track down who they are visiting and their probable location effectively. The evacuation teams can also access useful information about all your visitors which can be critical in saving their lives. They can also verify the identity of casualties based on the VMS data.
Embrace VMS for a Secure Workplace
Visitor management systems are becoming an integral element of a foolproof office security plan. You can keep a tight check on who is entering your building, stop unauthorized entries and access complete visitor information in a few simple clicks.
A VMS also cuts down paper use and helps you go green. You can also save costs by hiring extra staff as the VMS can be linked with self-service kiosks where the visitors can use an iPad/tablet interface for check-in.
We at Mobisoft offer a customizable iPad/tablet based visitor management solution that can be seamlessly deployed in no time in your office premise and add a robust digital security layer.
Feel free to talk to our experts to learn more about boosting your office security with a visitor management system.
Author's Bio

Nitin Lahoti is the Co-Founder and Director at Mobisoft Infotech. He has 15 years of experience in Design, Business Development and Startups. His expertise is in Product Ideation, UX/UI design, Startup consulting and mentoring. He prefers business readings and loves traveling.